Watchtower Password
Applies to: I41EJ The default password of the camera is “admin”. If you forgot the new password you had created, or you cannot log in with the default password “admin”, please reset your camera to. Sign Up Sign In. Forgot username or password Ryder and Ryder Logo are registered trademarks of Ryder System, Inc. Copyright © 1996 - 2017 Ryder System, Inc.
Watchtower supports private Docker image registries. In many cases, accessing a private registryrequires a valid username and password (i.e., credentials). In order to operate in such anenvironment, watchtower needs to know the credentials to access the registry.
The credentials can be provided to watchtower in a configuration file called config.json.There are two ways to generate this configuration file:
- The configuration file can be created manually.
- Call
docker login <REGISTRY_NAME>and share the resulting configuration file.
Create the configuration file manually¶
Create a new configuration file with the following syntax and a base64 encoded username andpassword auth string:
<REGISTRY_NAME> needs to be replaced by the name of your private registry(e.g., my-private-registry.example.org)
The required auth string can be generated as follows:
ℹ️ Username and Password for GCloud¶
For gcloud, we'll use _json_key as our username and the contentof gcloudauth.json as the password.bashecho -n '_json_key:$(cat gcloudauth.json)' | base64 -w0When the watchtower Docker container is started, the created configuration file(<PATH>/config.json in this example) needs to be passed to the container:
Share the Docker configuration file¶
To pull an image from a private registry, docker login needs to be called first, to get accessto the registry. The provided credentials are stored in a configuration file called <PATH_TO_HOME_DIR>/.docker/config.json.This configuration file can be directly used by watchtower. In this case, the creation of anadditional configuration file is not necessary.
When the Docker container is started, pass the configuration file to watchtower:
When creating the watchtower container via docker-compose, use the following lines:
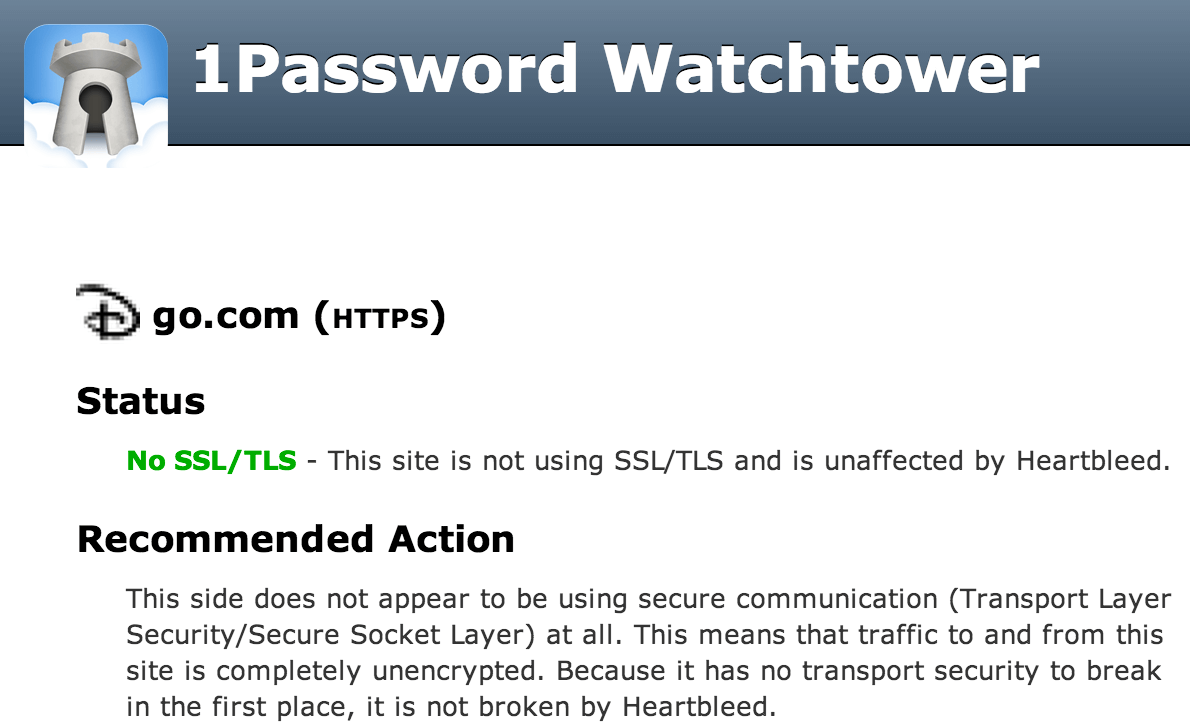
Watchtower Password Manager


Docker Config path¶
By default, watchtower will look for the config.json file in /, but this can be changed by setting the DOCKER_CONFIG environment variable to the directory path where your config is located. This is useful for setups where the config.json file is changed while the watchtower instance is running, as the changes will not be picked up for a mounted file if the inode changes.Example usage:
Credential helpers¶
Some private Docker registries (the most prominent probably being AWS ECR) use non-standard ways of authentication.To be able to use this together with watchtower, we need to use a credential helper.
To keep the image size small we've decided to not include any helpers in the watchtower image, instead we'll put thehelper in a separate container and mount it using volumes.
Example¶
Example implementation for use with amazon-ecr-credential-helper:

Use the dockerfile below to build the amazon-ecr-credential-helper,in a volume that may be mounted onto your watchtower container.
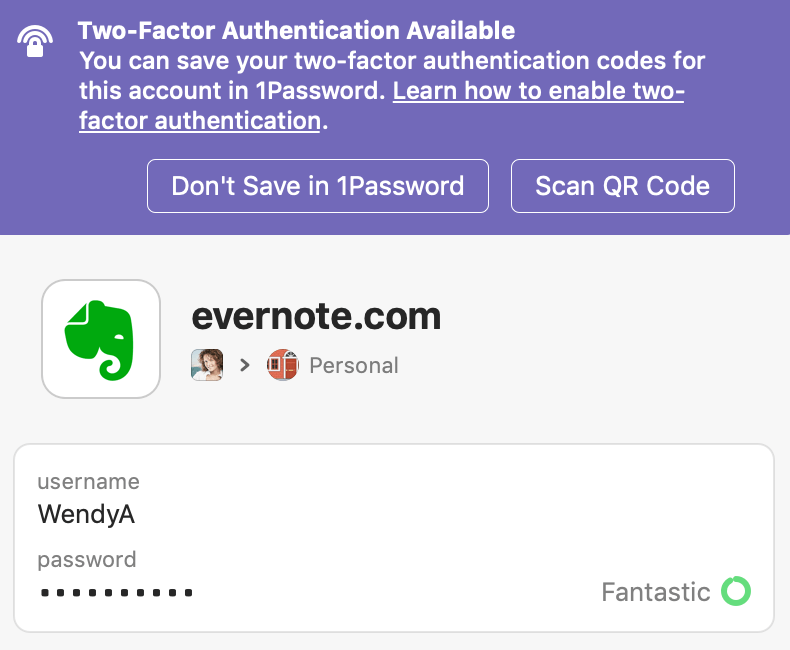
Watchtower 1password
- Create the Dockerfile (contents below):
- Use the following commands to build the aws-ecr-dock-cred-helper and store it's output in a volume:
```shell script
docker volume create helper
docker build -t aws-ecr-dock-cred-helper .
docker run -d --rm --name aws-cred-helper --volume helper:/go/bin aws-ecr-dock-cred-helper
- Create a docker-compose file (as an example) to help launch the container:
and the docker-compose definition:
A few additional notes:
- With docker-compose the volume (helper, in this case) MUST be set to
external: true, otherwise docker-compose will preface it with the directory name. - Note that 'credsStore' : 'ecr-login' is needed - and in theory if you have that you can remove the credHelpers section
- I have this running on an EC2 instance that has credentials assigned to it - so no keys are needed; however, you may need to include the
AWS_ACCESS_KEY_IDandAWS_SECRET_ACCESS_KEYenvironment variables as well. - An alternative to adding the various variables is to create a ~/.aws/config and ~/.aws/credentials files and place the settings there, then mount the ~/.aws directory to / in the container.
